Top 10 Hacking Tools - Dark Hacker Style
Concise, technical, and polished - this page explains 10 widely used hardware tools for security research and lab work. Each gadget section includes what it does, practical research uses, quick buying/setup tips, and a large image so the post looks premium on desktop and mobile.
- 1. Raspberry Pi - Lab Orchestration Node
- 2. Rubber Ducky - Keystroke Emulation
- 3. Flipper Zero - Multi-protocol Pocket Tool
- 4. Proxmark3 - RFID/NFC Research
- 5. Wi-Fi Pineapple - Wireless Assessment
- 6. Alfa Network Cards - High-power Wi-Fi Adapters
- 7. Ubertooth One - Bluetooth Research
- 8. Yardstick One - Sub-GHz RF Transceiver
- 9. Bus Pirate - Embedded Protocol Debugger
- 10. LAN Turtle - Internal Appliance
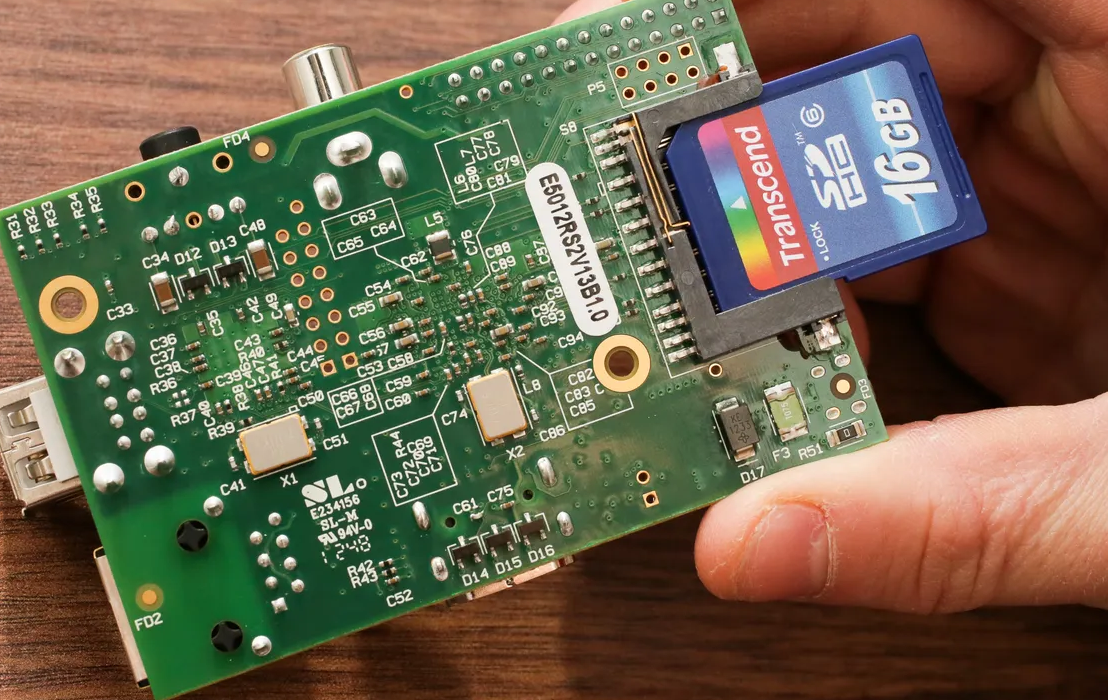
1. Raspberry Pi - Miniature Lab Server & Orchestration Node
The Raspberry Pi (Pi 4 / Pi 5) is the backbone for compact labs: low-cost, container-friendly, and versatile. Use it for logging stacks, lightweight services, sensor aggregation, or as a jump-box inside isolated networks.
Practical uses
- Honeypots and log collectors (in isolated environments).
- Local orchestration for capture tools and small CI jobs.
- Prototyping IoT testbeds and monitoring sensors.
Quick tip
Pick Pi 4+ for containers. Use reliable power and fast storage. Secure SSH with keys and keep images for rollbacks.
2. Rubber Ducky - Keystroke Emulation for Endpoint Assessment
Rubber Ducky emulates a keyboard to inject scripted keystrokes. In controlled environments it’s an efficient way to test endpoint detection for rapid automated input scenarios.
Practical uses
- Endpoint detection validation.
- Physical access policy testing.
Quick tip
Keep payloads benign and document every test run.

3. Flipper Zero - Pocket Multi-Protocol Tool
Flipper Zero supports RFID, NFC, infrared, sub-GHz, and GPIO. It’s compact and great for quick prototyping or protocol exploration in a lab workflow.
Practical uses
- Protocol learning and token auditing.
- Infrared command and simple radio experiments.
Quick tip
Use official firmware or vetted releases; log every scan for traceability.

4. Proxmark3 - Advanced RFID & NFC Research Station
Proxmark3 provides deep access to many RFID/NFC families and is the choice for protocol-level research and detailed signal analysis.
Practical uses
- Detailed tag analysis and protocol comparison.
- Designing mitigation recommendations for weak deployments.

5. Wi-Fi Pineapple - Wireless Assessment & Rogue AP Simulation
Wi-Fi Pineapple simplifies wireless recon and rogue AP scenarios - ideal for training defenders and validating segmentation in controlled ranges.
Practical uses
- Rogue AP simulation for detection exercises.
- Client profiling and wireless policy testing.

6. Alfa Network Cards - High-Power Wi-Fi Adapters
Alfa adapters bring better antennas and driver support for monitor mode and packet injection - staples in wireless labs where range and reliability matter.
Practical uses
- Packet capture, replay testing, and range experiments on segmented testbeds.

7. Ubertooth One - Bluetooth Development & Monitoring Dongle
Ubertooth helps analyze BLE advertisements, pairing flows, and stack behavior - useful for firmware hardening and interoperability debugging.
Practical uses
- Device pairing flow analysis and telemetry capture.

8. Yardstick One - Sub-GHz RF Transceiver
Yardstick One targets sub-GHz protocols used by remotes and IoT modules. It’s great for modulation and protocol study within controlled testbeds.
Practical uses
- Protocol analysis and modulation experiments (receive-focused unless authorized).

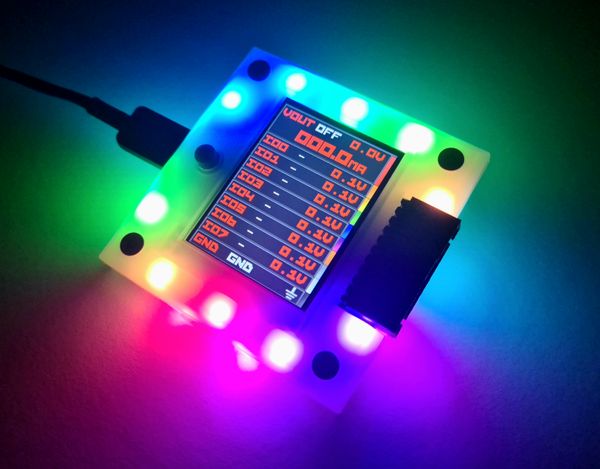
9. Bus Pirate - Universal Interface for Embedded Debugging
Bus Pirate exposes hardware buses to a host for firmware extraction and low-level debugging on devices you control - a must for embedded security work.
Practical uses
- UART/SPI/I2C inspection during firmware update flows and bootloader analysis.
10. LAN Turtle - Tiny Internal Appliance
LAN Turtle is compact and useful for internal diagnostics and permitted persistence simulations - often used by admins or within sanctioned red-team scopes.
Practical uses
- Telemetry collection, remote troubleshooting, and sanctioned simulations.

How to choose the right gear for your lab
Match gear to specialization:
- Wireless: Alfa + Wi-Fi Pineapple + Ubertooth.
- RFID / Access: Proxmark3 + Flipper Zero.
- Embedded: Raspberry Pi + Bus Pirate + logic analyzer.
- Endpoint / Physical: Rubber Ducky + LAN Turtle (sanctioned only).
Document tests, use isolated environments, and keep recovery/rollback procedures.
FAQ - Quick answers
Which tool is best to start with?
Begin with a Raspberry Pi, one Alfa adapter, and a Bus Pirate - then expand toward your speciality.
Need a gear list or custom lab plan? Contact us →All Rights Reserved © 2025 Codeila

